Cybercrime is no longer just a danger but they’re a part of day-to-day business life. Whether you run a small retail store, an expanding SME, or a big business in Singapore, your systems hold important data. Attackers can easily access customer records, payment information, employee information, and internal files.
This is where VAPT, which is known by a large number of business people but do not completely understand what it is and can do. With VAPT, you can locate as well as correct security gaps before attackers exploit them. It helps you to identify your weaknesses and teaches you the way to close them.
This guide explains what VAPT is, and why it is essential, along with a clear difference between vulnerability assessment and penetration testing, and what to look for when selecting a provider in Singapore.
What is VAPT and Why Does It Matter?
VAPT is an acronym for Vulnerability Assessment and Penetration Testing. It uses a systematic approach to detect, analyse, and test security flaws in your systems.
To understand the VAPT meaning, understand into two parts:
- Vulnerability Assessment (VA) – Finds security weaknesses.
- Penetration Testing (PT) – Tries to exploit those weaknesses to see how serious they are.
Together, they form a complete security check.
It is just like checking the building. Look for shattered windows as well as locked doors whenever you carry out a vulnerability analysis. The penetration tests are made to get in through them. When combined, they tell you exactly where you are attacked and exactly how much damage an attacker could cause.
VAPT testing matters because:
- Cyber attacks are rising.
- Data breaches lead to financial loss.
- Downtime affects revenue.
- Reputation damage is hard to repair.
- Regulations require proper security measures.
Without VAPT testing, you rely on hope. With it, you rely on facts.
Why Singapore Businesses Need VAPT Testing
Data protection is extremely important in Singapore. Any business that gathers personal information must protect it. This includes health records, NRIC numbers, billing information, and customer contact information. When there’s a breach, the effect can be quite severe.
- Regulatory penalties
- Legal claims
- Loss of customer trust
- Public scrutiny
- Operational disruption
VAPT testing helps to reduce these risks. Let’s understand some of the key reasons why Singapore companies should take VAPT seriously, as defined below:
1. Protection of Customer Data
Customers expect their information to remain private as breach damages trust. But VAPT testing helps you identify weak areas before attackers do.
2. Regulatory Compliance
There are security standards or rules that have to be followed in industries. Financial services, healthcare, and government vendors face greater scrutiny. There are strong security measures expected even in case you aren’t in a regulated industry.
Understanding the VAPT meaning helps business owners to see that it is not just technical work, but it also supports compliance and governance.
3. Business Continuity
Ransomware attacks can stop operations for days or weeks, and systems may become unusable. A proper VAPT process reduces the chance of such incidents.
4. Third-Party Risk Management
Many organisations require vendors to undergo VAPT testing before signing contracts. If you work with larger companies, they may request proof of testing.
5. Stronger Security Culture
Regular testing builds awareness. It sends a clear message that security is part of the business strategy.
In short, VAPT testing is not only about preventing attacks but also protecting your future.
Vulnerability Assessment vs Penetration Testing
One of the most common questions is about vulnerability assessment vs penetration testing. Many people think they mean the same thing, but they are different. Let’s understand in more depth below:
What’s Vulnerability assessment?
A vulnerability assessment will look at your systems for identified weaknesses and suggest remedial actions. These may include:
- Outdated software
- Patches are lacking
- Weak configurations
- Open ports
- Servers that were misconfigured
The objective is to produce a list of known vulnerabilities. The severity of each issue is sorted by its category. This can help your team prioritise issues more effectively. Vulnerability assessments usually are broad, but they concentrate on coverage.
What’s Penetration testing?
Penetration testing simulates a genuine attack as it goes deeper. The tester is attempting to take advantage of a flaw to get access. This may involve:
- Trying to get access to restricted data
- Escalating user privileges
- Extracting and identifying sensitive information
- Bypassing the authentication controls
- Impact concentrates on penetration tests.
You have to keep in mind the following in case you’re looking at and contrasting:
- vulnerability assessment with penetration testing
- An evaluation of vulnerability uncovers weaknesses.
It’s been proven by penetration tests exactly how dangerous they can be.
Read More: VAPT Services in Singapore: How to Protect Your Business from Real Cyber Threats
Vulnerability Assessment vs Penetration Testing – Key Differences
To understand the difference between vulnerability assessment and penetration testing, it helps to compare them clearly.
Scope
- The vulnerability evaluation consists of a broader scanning across systems as well as applications.
- Testing for penetration concentrates on the simulation of an aggressive attack.
Depth
- An evaluation of vulnerability detects potential risks.
- Testing by penetration confirms whether those dangers could be taken advantage of.
Approach
- The evaluation of vulnerability is generally automated.
- Penetration testing involves manual procedures as well as deeper analysis.
Outcome
- A vulnerability assessment provides you with a list of problems with severity levels.
- Penetration testing exhibits attack paths and real-world impact.
In practice, depending on only one is not enough. That is why VAPT combines both approaches. Together, they provide a full picture.
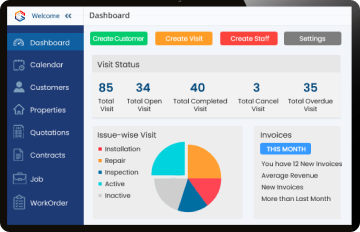
What are the VAPT Process Steps?
Understanding the VAPT process steps helps business owners know what to expect. A typical VAPT engagement follows a structured path.
1. Scoping
The first step defines what will be tested. This includes:
- Websites
- Applications
- Servers
- Networks
- Cloud environments
A clear scope prevents disruption and ensures focused testing.
2. Information Gathering
Testers collect data about the target systems. This may include domain details, network ranges, and exposed services.
3. Vulnerability Identification
This stage identifies weaknesses in the systems. It forms the foundation of VAPT testing.
4. Exploitation
This is where penetration testing begins. Testers attempt to exploit vulnerabilities to determine their impact.
5. Risk Analysis
Each finding is analysed and rated. The risk level depends on:
- Severity
- Likelihood of exploitation
- Potential business impact
6. Reporting
A detailed report is prepared. It includes:
- Executive summary
- Technical findings
- Risk ratings
- Remediation guidance
7. Remediation and Retesting
After fixes are applied, retesting confirms that vulnerabilities are resolved.
These VAPT process steps form part of a larger cycle known as the lifecycle.
How to Choose a VAPT Service Provider in Singapore
Choosing the right provider is important. Not all VAPT services offer the same quality. Here are key factors to consider.
1. Clear Methodology
A reliable provider should explain their VAPT process clearly. You should understand what they will test and how.
2. Experience with Singapore Businesses
Local knowledge matters. Providers should understand regulatory expectations and industry standards.
3. Detailed Reporting
A good report includes:
- Clear risk descriptions
- Evidence of exploitation
- Practical remediation steps
- Business impact explanations
Reports should be easy for both technical and non-technical stakeholders to understand.
4. Confidentiality
Security testing involves sensitive data. Ensure the provider follows strict confidentiality practices.
5. Retesting Support
VAPT testing should not end with a report. The provider should support retesting after remediation.
6. Transparent Pricing
Costs depend on scope, complexity, and environment size. Avoid providers who offer fixed prices without reviewing your systems.
When reviewing proposals, ask how they handle the VAPT lifecycle and whether they provide guidance beyond the test.
Conclusion
Even Singapore’s small businesses are at risk of cyberattacks. Nowadays, organisations need to be aware of VAPT and comprehend it so that they can take a hands-on approach to security instead of responding to harm that has already been done.
VAPT uses vulnerability analysis with penetration testing to offer visibility and real-life validation of risks. Businesses are able to remain secure while their systems are designed and updated by following the recognised VAPT process and maintaining a continuous VAPT lifecycle.
The normal VAPT testing is now a lot more than simply a technical exercise in the electronic world. This is a practical step in the direction of long-term stability, trust, and data security for your business.